Write Up for Malware Analysis CTF created by @Bowflexin91 & @HBRH_314
Register here: https://t.co/NT6T6u1x93
Don’t Break the Bank
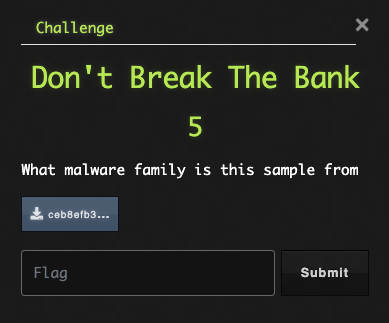
It’s time again to refer to our trusty OSINT tools. I’m going to use VirusTotal, yet again. After searching the hash, we can check the Community tab for some identification details.
Flag: Redaman
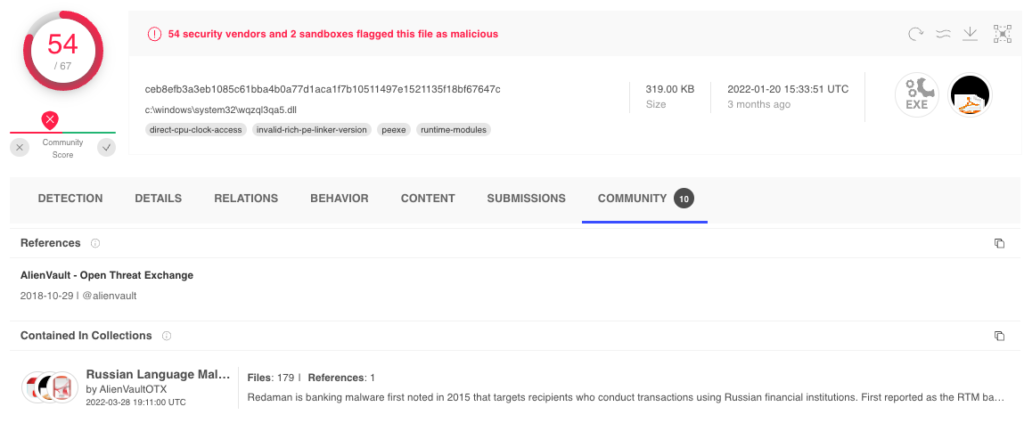
Heatdeath
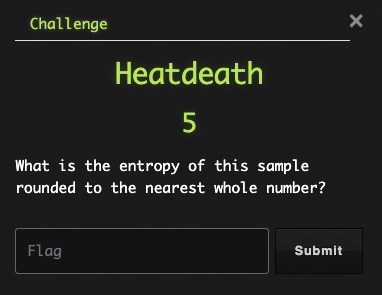
We need to determine the Entropy value of this sample….. what is Entropy?
Practical Security Analytics blog has this to say:Entropy is a measure of randomness within a set of data. When referenced in the context of information theory and cybersecurity, most people are referring to Shannon Entropy. This is a specific algorithm that returns a value between 0 and 8 were values near 8 indicate that the data is very random, while values near 0 indicate that the data is very homodulous.Shannon entropy can be a good indicator for detecting the use of packing, compression, and encryption in a file. Each of the previously mentioned techniques tends to increase the overall entropy of a file.
OK, well it just so happens that PeStudio will generate Entropy of this sample for us. We will pop on over to our sandbox and open this sample. In the main section, there will be an entropy value. Be sure to round it to the nearest whole number as the directions indicate.
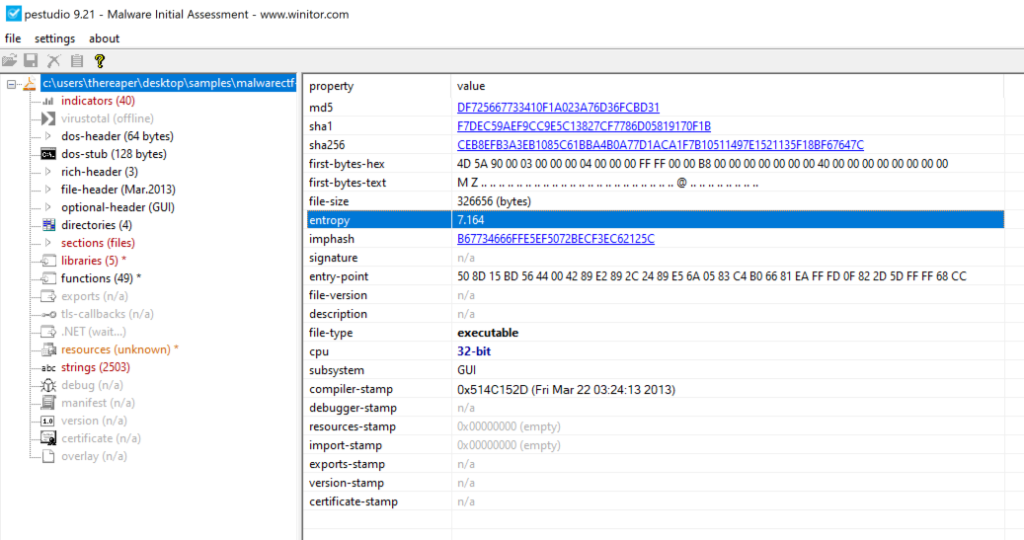
Flag: 7
Location, Location, Location
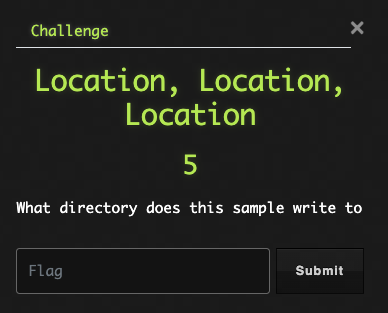
To determine what directories and files this sample writes, we will need dynamic analysis. That info can be found in VT on the Behavior tab. We see files written in the screenshot below. However, we only need the directory.
Flag: %TEMP%
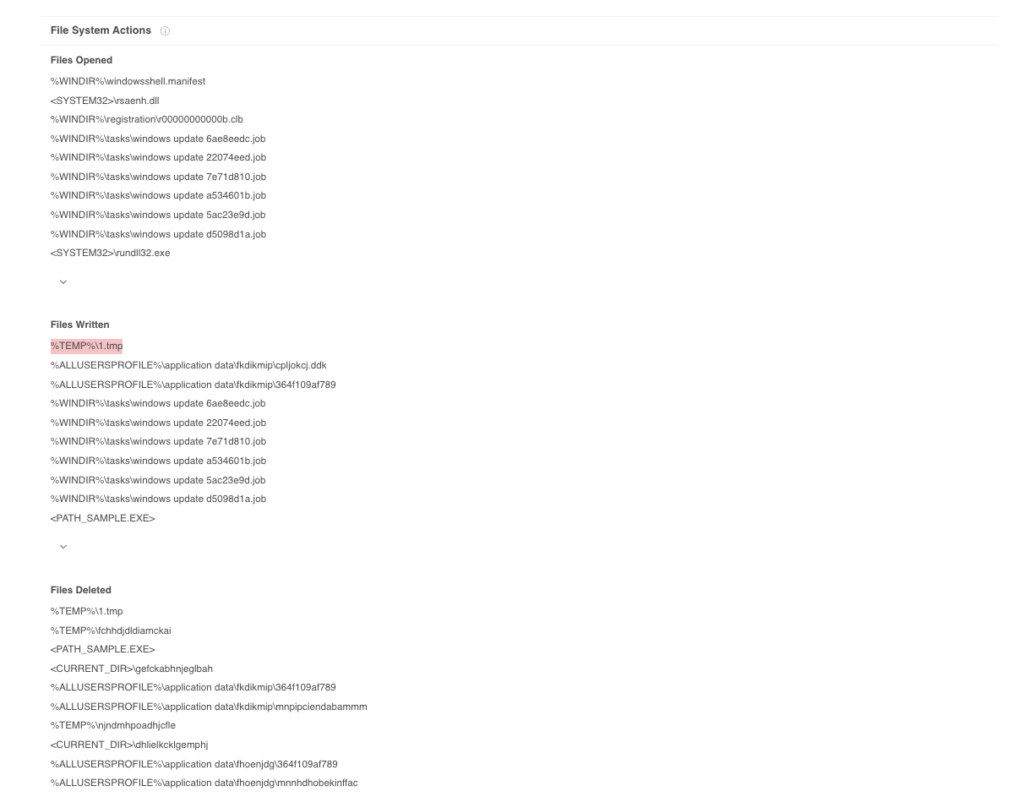
What’s Your Extension Again?
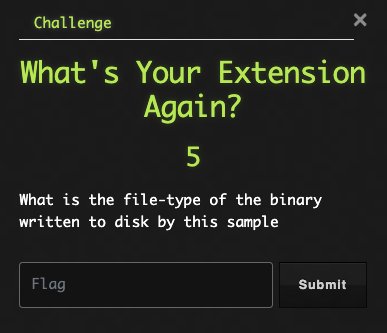
It’s time to do some OSINT research again, but VT didn’t have a lot of info regarding the dropped files. Never fear, we can ask the Google Box. I was able to locate an Any.run sandbox detonation that contains a lot of useful information.
Under the Dropped Files section, we can find the SHA256 hash of the file and then pivot to VT.
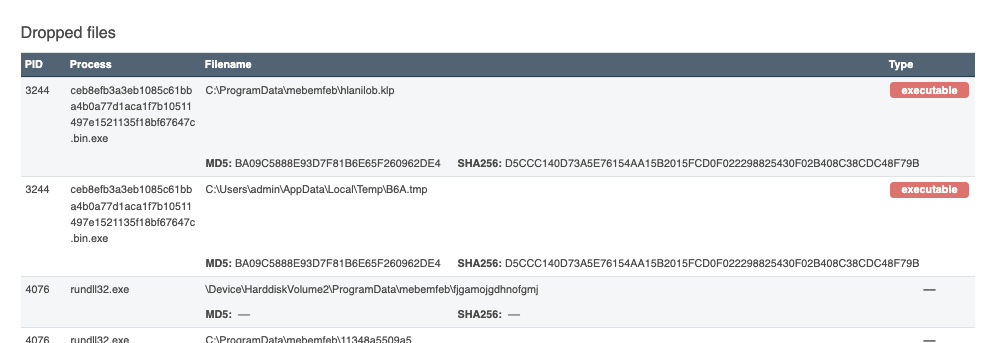
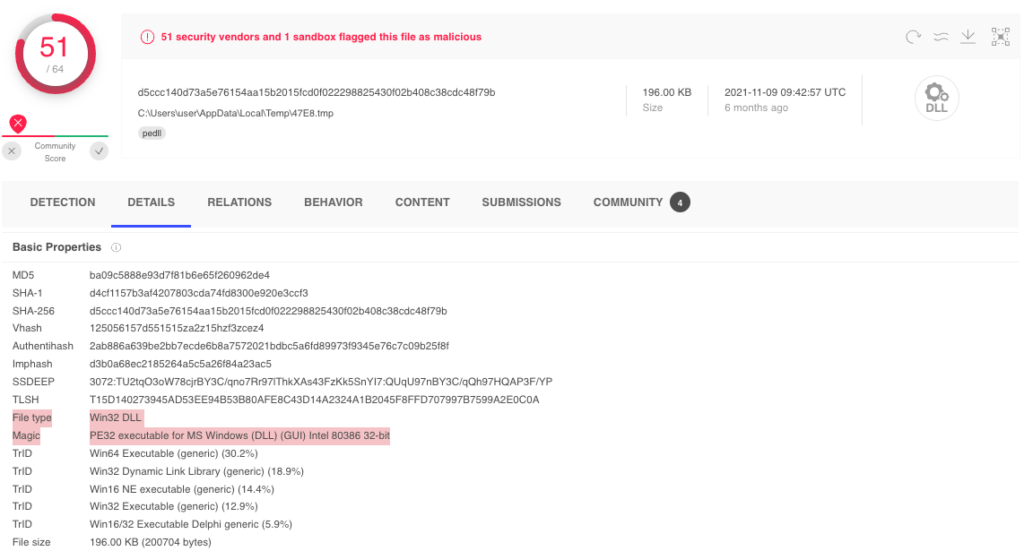
Flag: DLL
What’s Your Name Again?
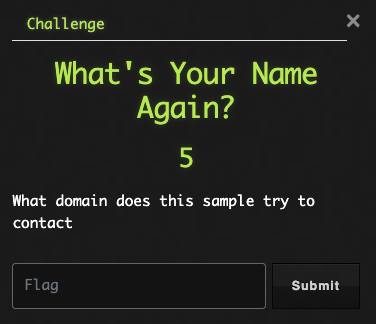
Back to the VT search Behavior tab for network related activity….
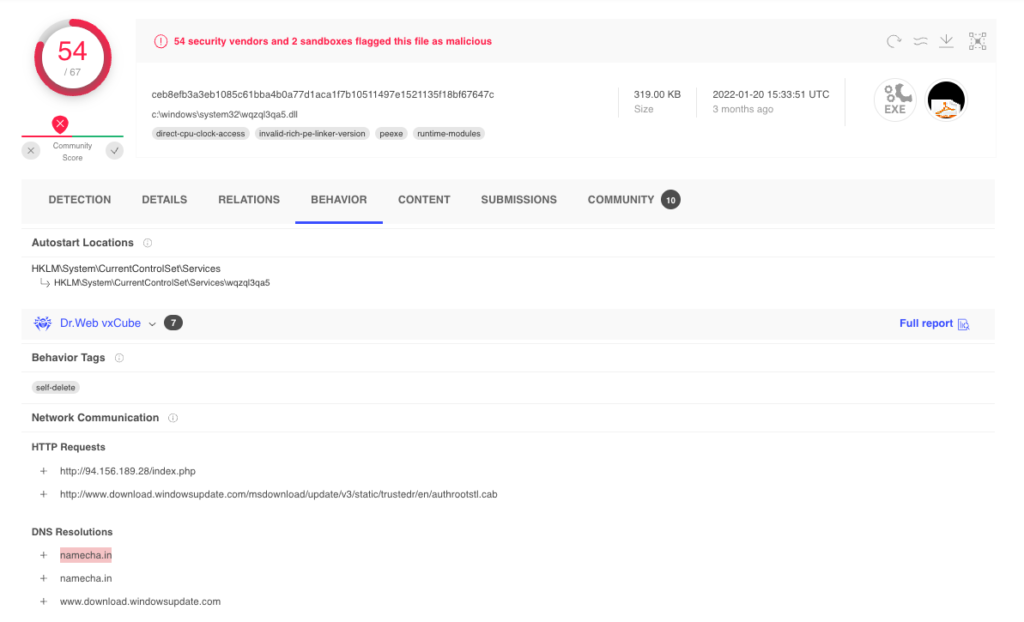
Flag: namecha.in
Sum Of All Things
Hey wait just a minute! Didn’t we already find the SHA value of the dropped file to look it up on VT? Would you look at that; two answers with one search.
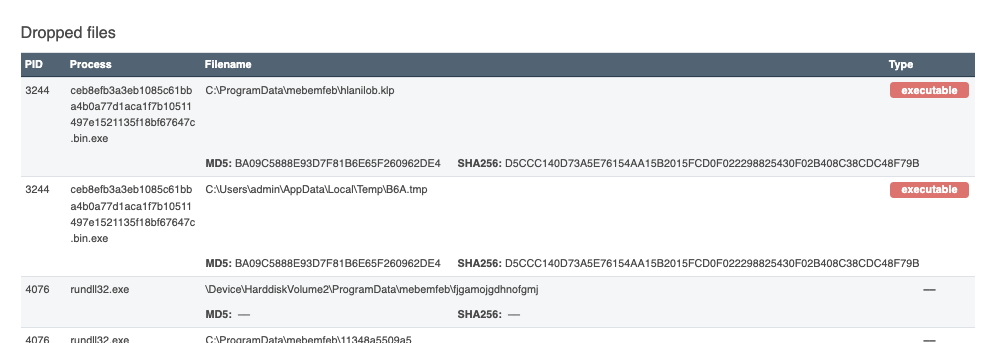
Flag: D5CCC140D73A5E76154AA15B2015FCD0F022298825430F02B408C38CDC48F79B
A Position Has Opened
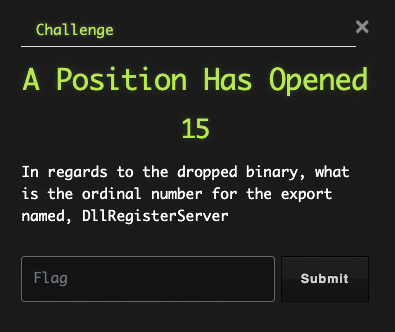
Now, we have to do some static analysis of the dropped file. We can download the sample from VT, and then, open it in PeStudio. The exports section will have the info we are looking for.
Flag: 4
Pulling On Your Strings
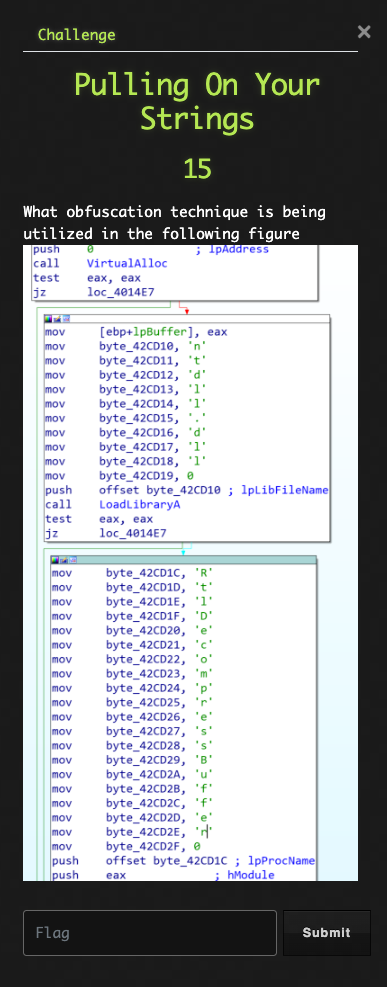
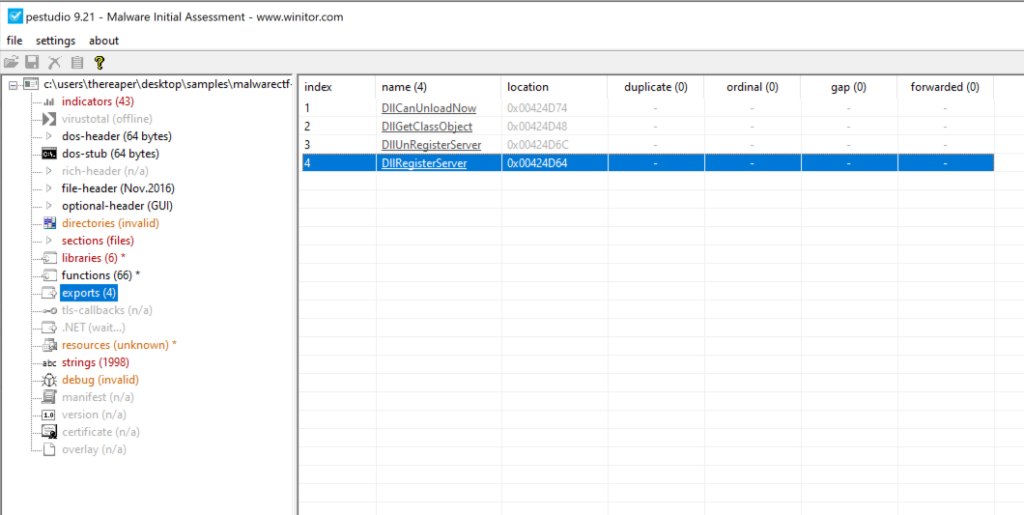
It appears we are looking for a proper name for this type of obfuscation technique. We seem to be looking at some type of string obfuscation, which would likely hide this data when reviewing the strings in the sample. Let’s take that idea and head over to ask Mr. Google that very question.
I was able to locate a nice article by Mandiant that explains the idea below.
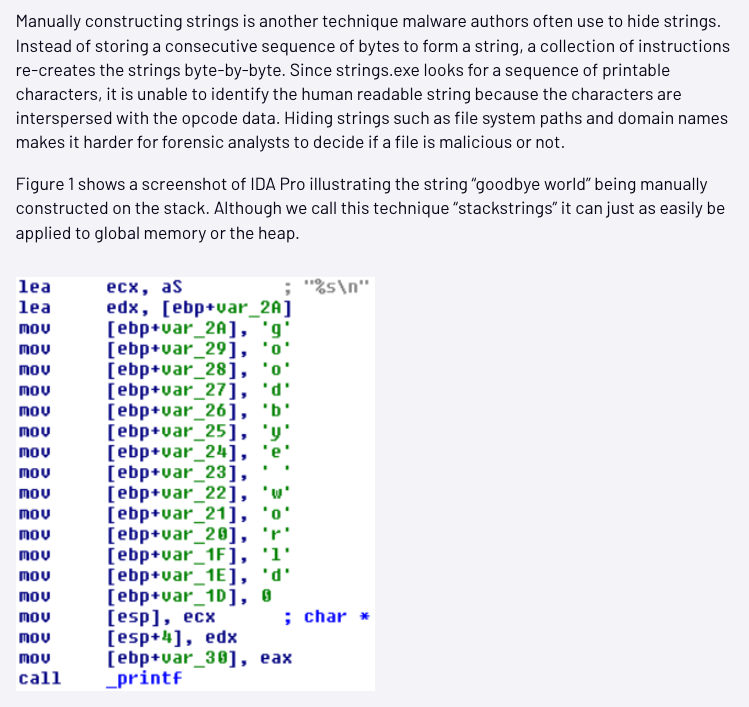
Mandiant refers to this as “stackstrings”. A little more searching gives me the flag.
Flag: Stack String
I Need My Space
VirtualAlloc is used to create an empty memory space to write data. Being able to identify where this new memory space resides can be quite helpful when debugging a sample. After doing some searching on the Interwebs, I found the below article that lays it out for us.
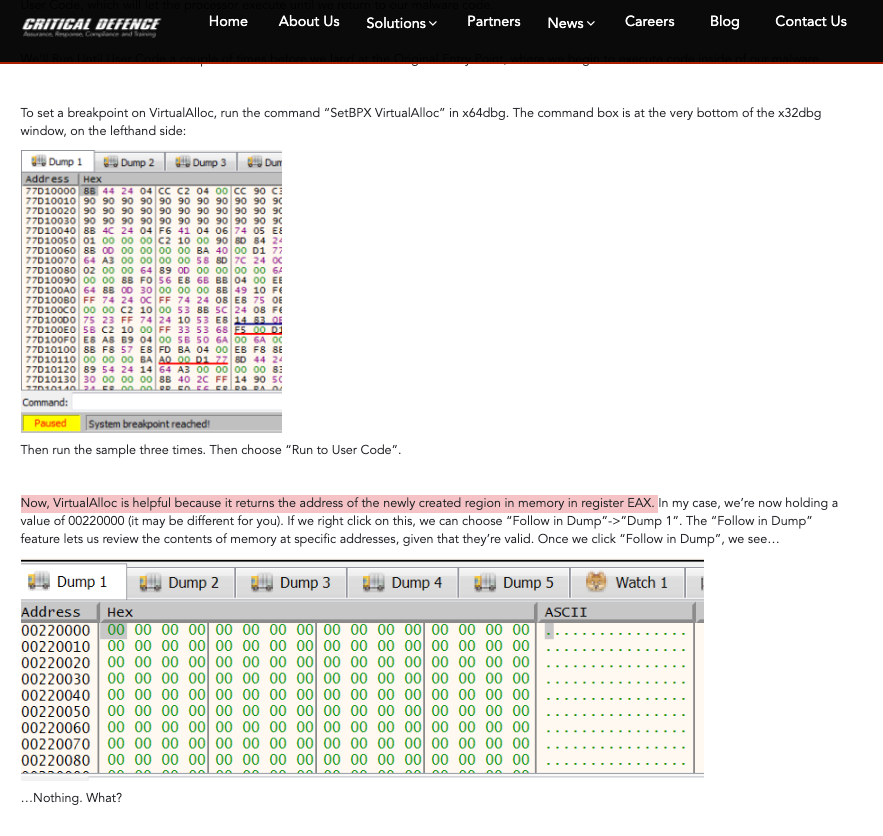
Flag: EAX